In the digital era of 2026, small businesses are no longer “flying under the radar” of cybercriminals. As automation and AI-driven attacks become more sophisticated, the need for robust cybersecurity best practices has transitioned from a technical luxury to a survival necessity. For a growing enterprise, a single data breach isn’t just a hurdle – it’s a potential shutdown.
At IT Work Solutions, we understand that small business owners need to focus on growth, not just firewalls. Whether you are leveraging our expert IT services to secure your cloud or our software development services to build secure applications, staying informed is your first line of defense. This guide outlines the essential cybersecurity best practices to protect your assets, your reputation and your future.
The 2026 Threat Landscape: Why Small Businesses are Targets
Many entrepreneurs believe that hackers only target giants with a high Market capitalization of Autodesk or massive conglomerates. However, the reality is that small businesses are often viewed as “soft targets” with weaker defenses. In 2026, we see a rise in “Ransomware-as-a-Service,” making it easier than ever for low-level criminals to launch attacks.
Implementing cybersecurity best practices is the only way to mitigate these risks. From securing your Automatic Data Processing workflows to ensuring your customer data is encrypted, a proactive stance is required. When you partner with IT Work Solutions, we integrate security into every layer of your business, ensuring your digital marketing services and sales funnels remain untampered.
1. Zero Trust Architecture: Trust No One, Verify Everything
The “Zero Trust” model is one of the most effective cybersecurity best practices today. It assumes that threats can exist both outside and inside the network. In a Zero Trust environment, every user and device must be authenticated and authorized before gaining access to data.
By utilizing expert IT services, you can implement micro-segmentation, ensuring that even if one employee’s device is compromised, the attacker cannot move laterally to access your sensitive payroll or Automatic Data Processing systems. This “never trust, always verify” approach is a cornerstone of modern defense.
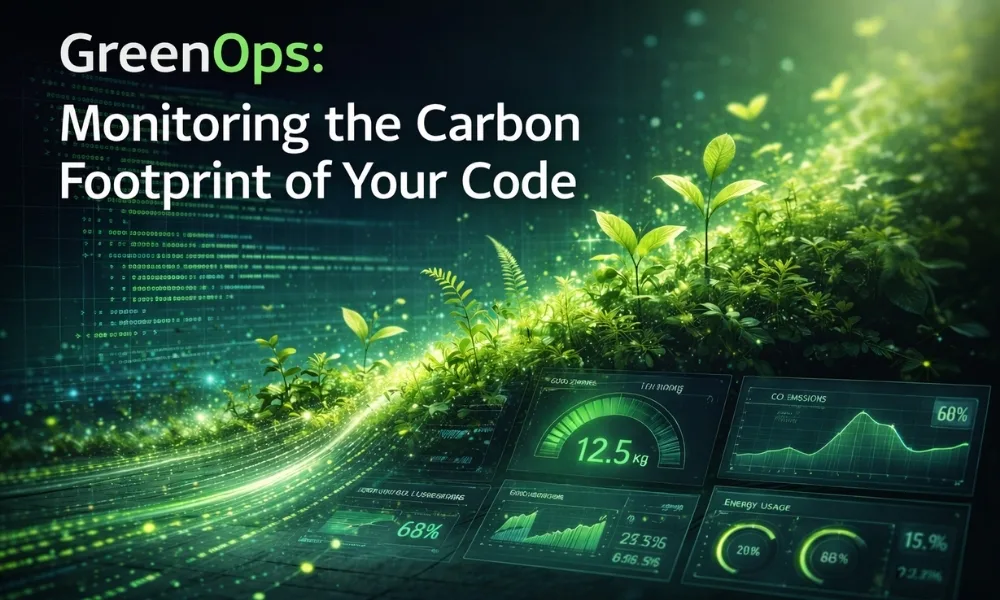
2. Secure Coding and Software Development Services
If your business develops internal tools or customer-facing apps, security must start at the source code. Vulnerabilities in unoptimized code are an open door for hackers. This is where professional software development services become invaluable.
Cybersecurity best practices in development include:
- Static and Dynamic Testing: Scanning code for vulnerabilities during the build.
- Dependency Management: Ensuring third-party libraries aren’t outdated or malicious.
- API Security: Protecting the “bridges” between your different software systems.
At IT Work Solutions, our software development services prioritize “Security by Design,” ensuring that your platform is as impenetrable as a high-security vault.
3. Employee Training: Strengthening the Human Firewall
Even the best software cannot stop a human from clicking a malicious link. Social engineering and phishing remain the leading causes of breaches. One of the most critical cybersecurity best practices is continuous employee education.
Your team should be trained to recognize:
- AI-Generated Phishing: Highly convincing emails that mimic your brand’s tone.
- Deepfake Audio: Fraudulent calls pretending to be company executives.
- Smishing: Malicious links sent via SMS to company mobile devices.
When we provide expert IT services, we include simulated phishing tests to keep your staff sharp. A secure culture is the ultimate reinforcement for your digital perimeter.
4. Multi-Factor Authentication (MFA) and Biometrics
Password-only protection is officially dead in 2026. One of the simplest yet most effective cybersecurity best practices is the universal rollout of Multi-Factor Authentication (MFA).
Moving beyond SMS codes – which can be intercepted – to biometrics (fingerprint/face ID) or physical security keys significantly raises the bar for attackers. For businesses that rely on digital marketing services to manage client accounts, MFA ensures that your social media and ad accounts remain under your control, even if a password is leaked.
5. Protecting Your Digital Presence and Marketing Assets
Your brand’s online reputation is its most valuable asset. If your website is defaced or your customer list is stolen, the damage is catastrophic. This is why cybersecurity best practices must extend to your digital marketing services.
Hackers often target “shadow IT” – marketing tools or plugins that haven’t been vetted by IT professionals. At IT Work Solutions, we audit your marketing stack to ensure that every pixel, tracker and CRM integration is secure. Protecting the integrity of your digital marketing services ensures that your customers can trust every interaction they have with your brand.
6. The Financial and Legal Reality of Cybersecurity
In 2026, the cost of a breach isn’t just the ransom; it’s the legal fees and fines. Regulators are increasingly looking at whether businesses followed recognized cybersecurity best practices before a breach occurred.
Much like investors look at the Market capitalization of Autodesk to gauge stability, clients look at your security certifications to gauge trust. By investing in expert IT services, you aren’t just buying software; you are buying insurance for your brand’s longevity.
7. Automated Backups and Disaster Recovery
Data loss can happen through cyberattacks or simple hardware failure. A primary cybersecurity best practices rule is the “3-2-1” backup strategy: Three copies of your data, on two different media, with one copy off-site (cloud).
Our expert IT services include automated, encrypted backups that allow for “point-in-time” recovery. If a ransomware attack hits, we can restore your systems to a state from minutes before the infection, minimizing downtime and avoiding the need to pay criminals.
Cybersecurity Best Practices: Common Questions Answered
Q1: What are the top 3 cybersecurity best practices for small businesses?
The top three are: Implementing Multi-Factor Authentication (MFA), conducting regular employee security training and maintaining an updated, off-site backup of all critical data.
Q2: How does IT Work Solutions help with cybersecurity?
We offer comprehensive expert IT services that include network monitoring, Zero Trust implementation and secure software development services to ensure your business remains protected from all angles.
Q3: Is cybersecurity important for my digital marketing services?
Absolutely. If your marketing accounts or website are hacked, you lose customer trust and ad spend. We secure your digital marketing services by auditing third-party tools and securing access points.
Q4: Why is Automatic Data Processing a security concern?
Automatic Data Processing often involves sensitive employee and financial data. If these automated workflows are not secured with cybersecurity best practices, they can be manipulated or intercepted by bad actors.
Q5: How do I know if my business is being targeted?
In 2026, every business is being scanned by automated bots. Common signs of an active attack include unusual login attempts, slow system performance or unexpected password reset emails.
Conclusion: Securing Your Growth in 2026
The road to business success in 2026 is paved with digital opportunities, but it is also fraught with digital risks. Implementing cybersecurity best practices is no longer a choice – it is a responsibility you owe to your employees, your customers and yourself.
At IT Work Solutions, we are dedicated to being your partner in this journey. From the foundation of secure software development services to the growth fueled by our digital marketing services and the protection offered by our expert IT services, we cover every base.
By adhering to these cybersecurity best practices, you ensure that your business remains resilient, trustworthy and ready for whatever the future holds. Don’t wait for a breach to happen – take the first step toward a secure future today.